
Rust for Offensive and Defensive Security
Live On-Site / Live Virtual
Harness Rust for Security Engineering
Learn fundamentals of writing Rust code for offensive security tools and harness the power of Rust to write memory-safe code. Build practical security tools from scratch.
What You Will Learn
Rust has rapidly become the language of choice for security tooling, offering memory safety guarantees without sacrificing performance. This course takes you from Rust fundamentals through building production-quality offensive and defensive security tools. You will learn how Rust's ownership model eliminates entire classes of vulnerabilities like buffer overflows, use-after-free, and data races -- and how to leverage these guarantees when building tools that need to be both reliable and fast.
On the offensive side, you will build port scanners, reverse shells, C2 framework components, and process injection tools. On the defensive side, you will create log analysis engines, file integrity monitors, network traffic analyzers, and threat detection systems. Every tool is built from scratch with an emphasis on understanding the underlying systems programming concepts.
The course also covers cross-platform development targeting Windows, Linux, and macOS, along with practical considerations for packaging, distribution, and evasion. By the end, you will have a portfolio of working security tools and the Rust expertise to build more on your own.
Key Objectives
- ✓Master Rust ownership, borrowing, lifetimes, and error handling for security applications
- ✓Understand unsafe Rust and Foreign Function Interface (FFI) for systems integration
- ✓Build TCP/UDP network tools with async programming using Tokio
- ✓Develop offensive tools including port scanners, reverse shells, and C2 components
- ✓Implement process injection and credential harvesting techniques in Rust
- ✓Build defensive tools for log analysis, YARA integration, and file integrity monitoring
- ✓Create network monitoring and threat detection systems
- ✓Cross-compile security tools for Windows, Linux, and macOS targets
- ✓Package and distribute Rust-based security tooling
- ✓Apply evasion considerations for offensive tool development
All our live trainings are highly customizable. We can tailor the content to cover topics specific to your team's needs. Contact us for more details.
Syllabus
Module 1: Rust Fundamentals for Security +
- •Ownership, borrowing, and lifetimes
- •Error handling with Result and Option types
- •Structs, enums, traits, and generics
- •Unsafe Rust and raw pointers
- •Foreign Function Interface (FFI) for C interop
- •Cargo, crates, and dependency management
Module 2: Network Programming +
- •TCP and UDP socket programming
- •Building HTTP clients and servers
- •Protocol implementation and parsing
- •Async networking with Tokio runtime
- •TLS/SSL implementation in Rust
- •Raw packet crafting and manipulation
Module 3: Offensive Tooling +
- •Building multi-threaded port scanners
- •Reverse shell development and encrypted channels
- •C2 framework component design
- •Process injection techniques on Windows and Linux
- •Credential harvesting and extraction tools
- •Shellcode loaders and payload delivery
Module 4: Defensive Tooling +
- •Log analysis and event correlation engines
- •YARA rule integration for malware detection
- •File integrity monitoring systems
- •Network traffic monitoring and anomaly detection
- •Threat detection and alerting pipelines
- •Building a lightweight EDR agent
Module 5: Cross-Platform Development +
- •Targeting Windows, Linux, and macOS from a single codebase
- •Cross-compilation setup and toolchains
- •Platform-specific API access (Win32, POSIX)
- •Packaging and distribution strategies
- •Evasion considerations for offensive tools
- •Static analysis and binary hardening
Prerequisites
To successfully participate in this course, attendees should possess the following:
- • Basic understanding of cybersecurity concepts and networking fundamentals
- • Familiarity with at least one systems programming language (C, C++, Go, or similar)
- • Basic command-line proficiency on Linux or macOS
- • No prior Rust experience required -- fundamentals are covered in the course
Duration
2 Days
Ways To Learn
- Live Virtual
- Live On-Site
Who Should Attend?
Security professionals, developers interested in Rust for security tooling, and anyone looking to build memory-safe offensive/defensive tools.
Laptop Requirements
- • Laptop with 8+ GB RAM and 40 GB hard disk space
- • Cloud lab instances provided
- • Administrative access on the system
- • Setup instructions sent before the course
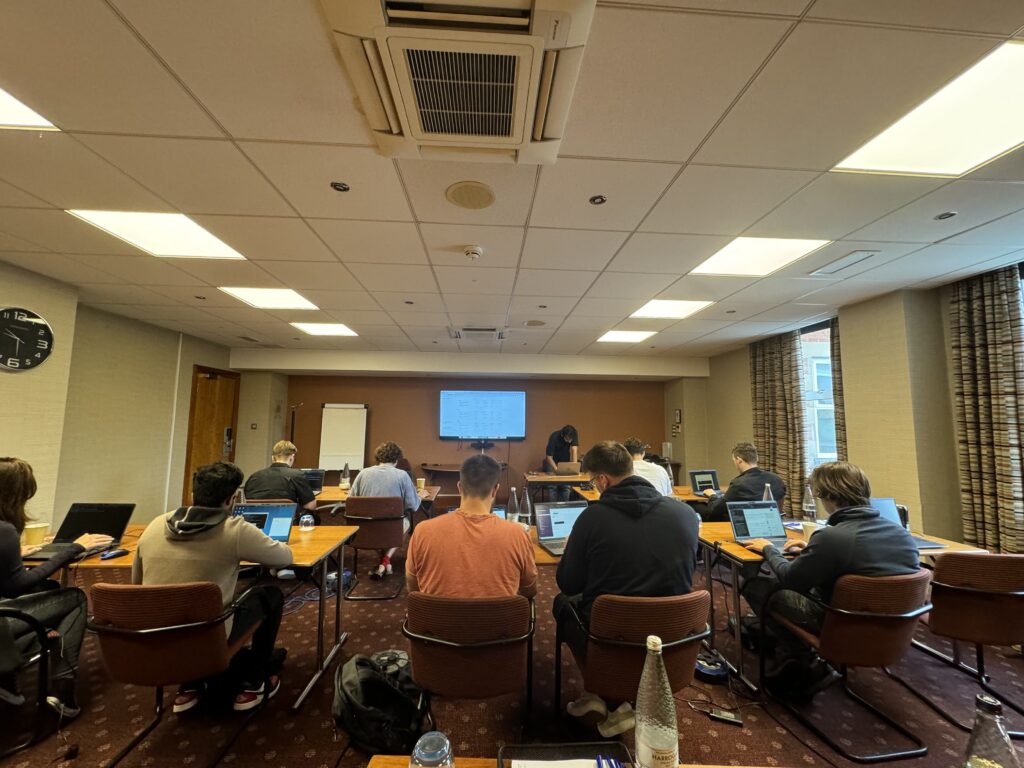
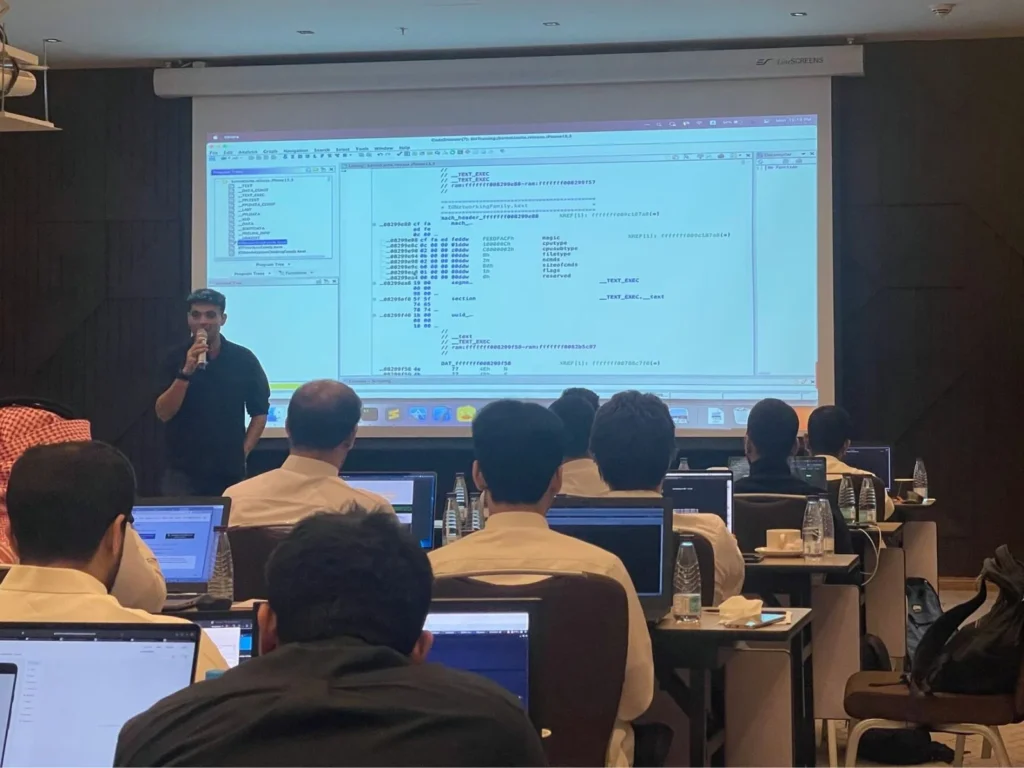
We Train Anywhere in the World
Can't make it to a public event? We deliver on-site training directly at your location. Our instructors travel worldwide — tell us where you are.
Your country not listed? We still travel there.
Get in TouchTrusted Training Providers
Our trainers boast more than ten years of experience delivering diverse training sessions at conferences such as Blackhat, HITB, Power of Community, Zer0con, OWASP Appsec, and more.






Take Your Skills To The Next Level
Our Modes Of Training
Live Virtual
Get in touch for pricing
Perfect for Teams in Multiple Locations
- Real-time interaction with expert trainers via Zoom
- Customizable content for your team
- Continued support after training
- Hands-on labs with cloud environments
Live On-Site
Get in touch for pricing
Perfect for Teams in One Location
- Real-time interaction at your onsite location
- Customizable content for your team
- Continued support after training
- Hands-on labs with cloud environments
FAQ
The information on this page is subject to change without notice.
Contact Us
Have a question or want to learn more about this training? Get in touch with us.
Our Location
51 Pleasant St # 843, Malden, MA, US, 02148
General Inquiries
contact@8ksec.io
Trainings
training@8ksec.io
