
Practical Mobile Application Exploitation
Live On-Site / Live Virtual / On-Demand
Master Mobile Application Security Testing
Learn various reversing techniques and bug categories for Android and iOS systems. This hands-on course covers comprehensive mobile application security testing, from static and dynamic analysis to advanced exploitation techniques using Frida and other industry-standard tools.

What You Will Learn
This practical course teaches you the essential skills needed to perform comprehensive security assessments of mobile applications on both iOS and Android platforms. You will learn how to set up a mobile pentesting environment, extract and analyze application binaries, and identify common vulnerability patterns that affect mobile apps in the real world.
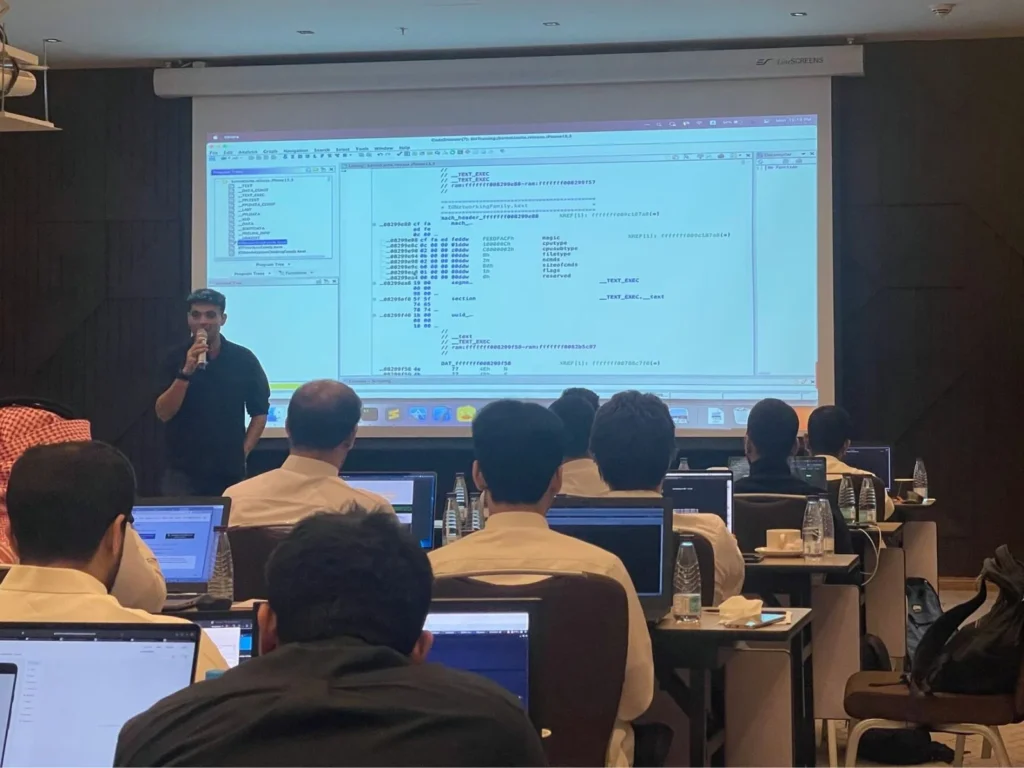
The course covers both static and dynamic analysis techniques, including reverse engineering with tools like Ghidra and Hopper, runtime manipulation with Frida, network traffic interception, and exploitation of common mobile application vulnerabilities such as insecure data storage, weak cryptography, and broken authentication mechanisms.
Through hands-on labs using vulnerable applications created specifically for this course and real-world application vulnerabilities, you will gain practical experience in discovering and exploiting security flaws. The course also covers defense strategies, helping you understand how to build more secure mobile applications.
Key Objectives
- ✓Set up your own lab environment for iOS and Android testing
- ✓Reverse engineer iOS and Android binaries (Apps and system binaries)
- ✓Get an understanding of the ARM64 instruction set
- ✓Learn Device Fingerprinting and Anti-Fraud techniques
- ✓Debug iOS and Android apps using lldb and other tools
- ✓Audit iOS and Android apps for security vulnerabilities
- ✓Understand and bypass anti-debugging and obfuscation techniques
- ✓Learn manual and automated ways of bypassing exploit mitigations
- ✓Identify vulnerabilities in native as well as cross-platform apps
- ✓Exploit different IPC mechanisms in iOS and Android applications
- ✓Get a detailed walkthrough on using IDA Pro, Hopper, Ghidra and other tools
- ✓Secure mobile apps by implementing custom solutions
- ✓Become a Certified Mobile Security Engineer (CMSE)
All our live trainings are highly customizable. We can tailor the content to cover topics specific to your team's needs. Contact us for more details.
Syllabus
Module 1: Introduction to Reverse Engineering in iOS +
- •Key Concepts and Terminologies
- •Introduction to Hopper/Ghidra
- •Introduction to the ARM64 instruction set
- •Introduction to Objective-C and Swift
- •Reversing Objective-C and Swift Binaries
- •Disassembling methods
- •Modifying assembly instructions
- •Deciphering Mangled Swift Symbols
- •Identifying Native Code
- •Understanding the Program flow
- •Identifying Cross-Platform mobile frameworks
Module 2: Getting Started with iOS Security +
- •iOS security model
- •App Signing, Sandboxing, and Provisioning
- •iOS App Groups
- •Primer to iOS 17-18 security
- •Xcode Primer
- •Address Sanitizer
- •Exploring the iOS filesystem
- •What's in a Code Signature?
- •Entitlements explained
- •How Sandboxing works on iOS
- •Setting up lldb for Debugging
- •lldb basic and advanced usage
- •Setting up the testing environment
- •Jailbreaking your device
- •What's in a Rootless Jailbreak?
- •Jailbreak Bootstraps
- •Sideloading apps
- •Binary protection measures
- •Decrypting IPA files
- •Self-signing iOS binaries
Module 3: Static and Dynamic Analysis of iOS Apps +
- •Bundle vs Data Container
- •Finding Secrets in Code
- •Dumping class information
- •Insecure local data storage
- •Inspecting Keychain items
- •Identifying URL schemes and Universal Links
- •Dynamic Analysis of iOS applications
- •Method Swizzling
- •Debugging apps using lldb
- •Modifying ARM registers
- •Basic App Instrumentation techniques using Frida
- •Advanced App Instrumentation techniques using Frida
- •Frida on Non-Jailbroken devices
- •Frida on Swift and native code
- •Reversing Third Party frameworks
- •Testing React Native and Flutter Apps
- •Automating App Inspection
Module 4: iOS Application Vulnerabilities +
- •Tracing Crypto operations
- •Side channel data leakage
- •Sensitive information disclosure
- •Bypassing Jailbreak Detection
- •Bypassing SSL Pinning
- •Bypassing Certificate transparency checks
- •Exploiting iOS WebViews
- •Exploiting URL schemes and Universal Links
- •Client-side injection
- •Bypassing jailbreak, piracy checks
- •Inspecting Network traffic
- •Traffic interception over HTTP, HTTPS
- •Manipulating network traffic
- •Identifying iOS malware
Module 5: Securing iOS Applications +
- •AppAttest and Device Check frameworks
- •Device Fingerprinting
- •Detecting GPS Spoofing
- •Implementing Secure Webviews
- •Code Obfuscation techniques
- •Protecting the Transport Layer
- •Detecting Malicious Libraries
- •Implementing Anti-Debug Checks
- •Detecting Suspicious Device Reset
- •Detecting Patched Applications
- •Detecting Proxied Applications
- •Jailbreak Detection Techniques
Module 6: Intro to Android Security +
- •Why Android
- •Android Security Architecture
- •Extracting APK files from Google Play
- •Understanding Android application structure
- •Signing Android applications
- •ADB – Non-Root
- •Rooting Android devices
- •ADB – Rooted
- •Understanding the Android file system
- •Permission Model Flaws
- •Attack Surfaces for Android applications
Module 7: Android Components +
- •Understanding Android Components
- •Introducing Android Emulator
- •Introducing Android AVD
- •Setting up Android Pentest Environment
Module 8: Reversing Android Apps +
- •Process of Android Apps Engineering
- •Reverse Engineering for Android Apps
- •Smali Learning Labs
- •Examining Smali files
- •Smali vs Java
- •Dex Analysis and Obfuscation
- •Reversing Obfuscated Android Applications
- •Exploiting Android Accessibility Permissions
- •Patching Android Applications
- •Reverse Engineering known complex Malware in the Wild and anti-evasion techniques
Module 9: Static and Dynamic Analysis +
- •Proxying Android Traffic
- •Introduction to Certificate Transparency
- •Exploiting Local Storage
- •Exploiting Weak Cryptography
- •Exploiting Side Channel Data Leakage
- •Multiple Manual and Automated Root Detection and Bypass Techniques
- •Exploiting Weak Authorization mechanism
- •Identifying and Exploiting Android Components
- •Analyzing Proguard, DexGuard, and other Obfuscation Techniques
- •Exploiting Android NDK
- •Exploiting Android WebViews
- •Exploiting DeepLinks in Android
- •Multiple Manual and Automated SSL Pinning Bypass techniques
- •Exploiting Flutter Applications
Module 10: Frida and Automated Exploitation +
- •Exploiting Crypto using Frida
- •Basic App Exploitation techniques using Frida
- •Dumping Class Information using Frida
- •Dumping Method Information using Frida
- •Viewing and Changing Information using Frida
- •Calling Arbitrary functions using Frida
- •Exploiting native libraries using Frida
- •Tracing using Frida
- •Advanced App Exploitation techniques using Frida
- •Frida on non-rooted Android
Module 11: Securing Android Apps +
- •Detecting Patched Android Applications
- •App Integrity Protection
- •Detecting Malicious Libraries
- •Detecting Emulator/Rooted Devices
- •Secure Implementation of WebViews
- •Implementing Anti-Debug Checks
- •Detecting Suspicious Device Reset
- •Detecting Proxied Applications
Prerequisites
To successfully participate in this course, attendees should possess the following:
- • Working knowledge of cybersecurity and pentesting fundamentals
- • Basic working knowledge of iOS and Android platforms
- • Basic Linux skills and command-line proficiency
- • Understanding of fundamental programming concepts and looping structures in at least one higher-level language (Java, Kotlin, Objective-C, Swift, C, C++, or similar)
- • Basic ARM/AARCH64 binary assembly knowledge is recommended, but not required
Certified Mobile Security Expert (CMSE)
This course prepares you for the CMSE certification exam, a hands-on assessment that tests your ability to find and exploit vulnerabilities in mobile applications across both iOS and Android platforms.
EXAM DURATION: 48 Hours
Learn More
Duration
2 Days
Ways To Learn
- On Demand
- Live Virtual
- Live On-Site
Who Should Attend?
This course is for penetration testers, mobile developers, security engineers, and anyone keen to learn mobile application security testing for both iOS and Android platforms.
Laptop Requirements
- • Laptop with: 8+ GB RAM and 40 GB hard disk space
- • Students will be provided with access to Linux cloud instances (Live On-site & Virtual Training only)
- • Students will be provided with access to Corellium for iOS and Android hands-on and as such do not need to carry physical devices (Live On-site & Virtual Training only)
- • Administrative access on the system
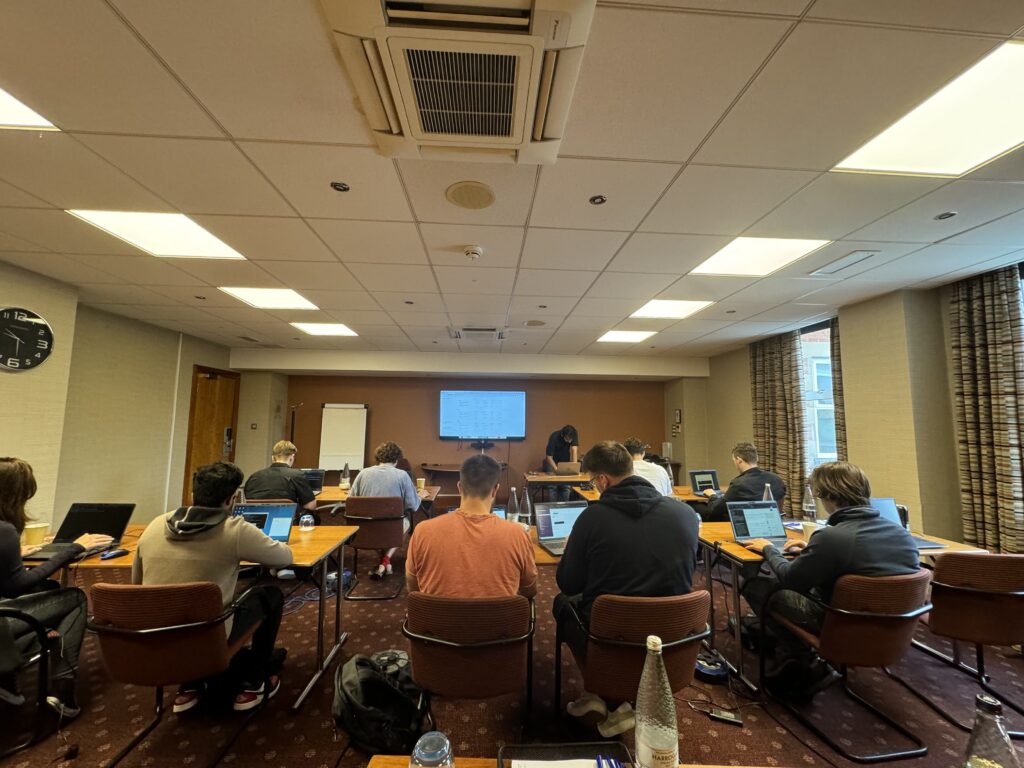
We Train Anywhere in the World
Can't make it to a public event? We deliver on-site training directly at your location. Our instructors travel worldwide — tell us where you are.
Your country not listed? We still travel there.
Get in TouchTrusted Training Providers
Our trainers boast more than ten years of experience delivering diverse training sessions at conferences such as Blackhat, HITB, Power of Community, Zer0con, OWASP Appsec, and more.






Take Your Skills To The Next Level
Our Modes Of Training
On Demand
Learn at your own pace
Perfect for Self-Paced Learners
- Immediate access to materials
- Lecture recordings and self-assessments
- 365 days of access
- Certificate of completion
- Dedicated email support
- Certification exam
Live Virtual
Get in touch for pricing
Perfect for Teams in Multiple Locations
- Real-time interaction with expert trainers via Zoom
- Customizable content for your team
- Continued support after training
- Certification exam
Live On-Site
Get in touch for pricing
Perfect for Teams in One Location
- Real-time interaction at your onsite location
- Customizable content for your team
- Continued support after training
- Certification exam
FAQ
The information on this page is subject to change without notice.
Contact Us
Have a question or want to learn more about this training? Get in touch with us.
Our Location
51 Pleasant St # 843, Malden, MA, US, 02148
General Inquiries
contact@8ksec.io
Trainings
trainings@8ksec.io
