
Offensive iOS Internals
Live On-Site / Live Virtual / On-Demand
Become a Certified iOS Security Researcher
Deep dive into iOS operating system architecture, memory management, application sandboxing, inter-process communication, code signing, and kernel internals. This hands-on course covers both userland and kernel-level security mechanisms.

What You Will Learn
This course provides an in-depth exploration of the iOS operating system, focusing on its security architecture and internals. You will learn about iOS memory management, application sandboxing, code signing mechanisms, entitlements, and advanced security mitigations including PAC, SPTM, PPL, and PAN. The course gives you a thorough understanding of how iOS protects itself from user-space to kernel-space.
On the application security side, you will learn to identify and exploit common iOS application vulnerabilities, including insecure data storage, broken cryptography, WebView exploitation, URL scheme abuse, and network traffic manipulation. You will use Frida for advanced dynamic instrumentation, hooking, and runtime manipulation of iOS applications.
The course dives deep into iOS kernel internals, covering the XNU kernel architecture, the Mach and BSD layers, IOKit, kernel extension analysis, and kernel vulnerability case studies. You will learn to symbolicate the iOS kernelcache, analyze kernel panic files, and understand advanced mitigations like SPTM and PPL.
Key Objectives
- ✓Understand the iOS security model, sandboxing, and code signing
- ✓Learn iOS memory management and exploit mitigations
- ✓Master Frida for iOS dynamic instrumentation and hooking
- ✓Exploit common iOS application vulnerabilities
- ✓Bypass jailbreak detection, SSL pinning, and other security checks
- ✓Understand XNU kernel architecture (Mach, BSD, IOKit)
- ✓Extract and analyze the iOS kernelcache and kexts
- ✓Understand advanced mitigations: PAC, SPTM, PPL, PAN
- ✓Analyze sandbox escape and entitlement validation vulnerabilities
- ✓Perform XPC and IPC vulnerability analysis
- ✓Implement iOS security hardening measures
- ✓Become a Certified iOS Security Researcher (CISR)
All our live trainings are highly customizable. We can tailor the content to cover topics specific to your team's needs. Contact us for more details.
Syllabus
Module 1: iOS Architecture & Security Model +
- •iOS filesystem and directory layout
- •Application sandboxing architecture
- •Code signing and provisioning profiles
- •Entitlements and their security implications
- •App groups and data sharing
- •Security mitigations overview (ASLR, DEP, PAC)
Module 2: iOS Debugging & Analysis +
- •lldb setup and advanced usage
- •Setting up the testing environment
- •Jailbreaking fundamentals and rootless jailbreaks
- •Sideloading applications
- •Binary protection measures
- •Decrypting IPA files
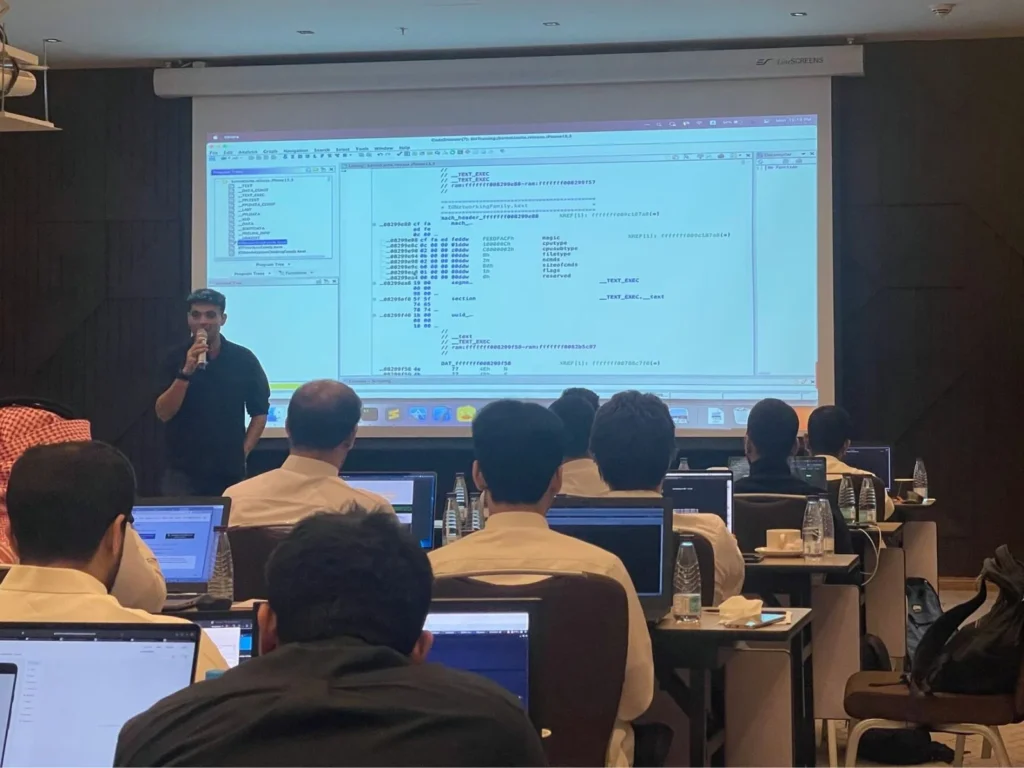
Module 3: iOS Kernel Internals +
- •XNU kernel architecture overview
- •Mach and BSD layers
- •IOKit driver framework
- •Kernelcache extraction and analysis
- •Kernel extension (kext) analysis
- •AMFI and CoreTrust deep dive
- •Sandbox profile analysis
- •PAC, SPTM, PAN, and PPL walkthrough
Module 4: Frida for iOS +
- •Frida overview and setup for iOS
- •Hooking Objective-C and Swift methods
- •Instrumenting native code
- •Memory manipulation techniques
- •Custom tracing and profiling
- •Frida-trace and handler development
Module 5: iOS Application Security +
- •Tracing crypto operations
- •Side channel data leakage exploitation
- •Bypassing jailbreak detection
- •Bypassing SSL pinning
- •Exploiting WebViews and URL schemes
- •Network traffic interception and analysis
Module 6: iOS Vulnerability Research +
- •Sandbox escape case studies
- •Entitlement validation vulnerabilities
- •XPC-related vulnerabilities
- •Kernel vulnerability walkthrough
- •PAC bypass case studies
- •Patch diffing iOS updates
Prerequisites
To successfully participate in this course, attendees should possess the following:
- • Working knowledge of cybersecurity fundamentals
- • Basic iOS/macOS familiarity
- • Basic command-line proficiency
- • Understanding of C/Objective-C/Swift basics helpful but not required
Certified iOS Security Researcher (CISR)
This course prepares you for the CISR certification exam, testing your knowledge of iOS internals and security.
EXAM DURATION: 24 Hours
Learn More
Duration
3 Days
Ways To Learn
- On Demand
- Live Virtual
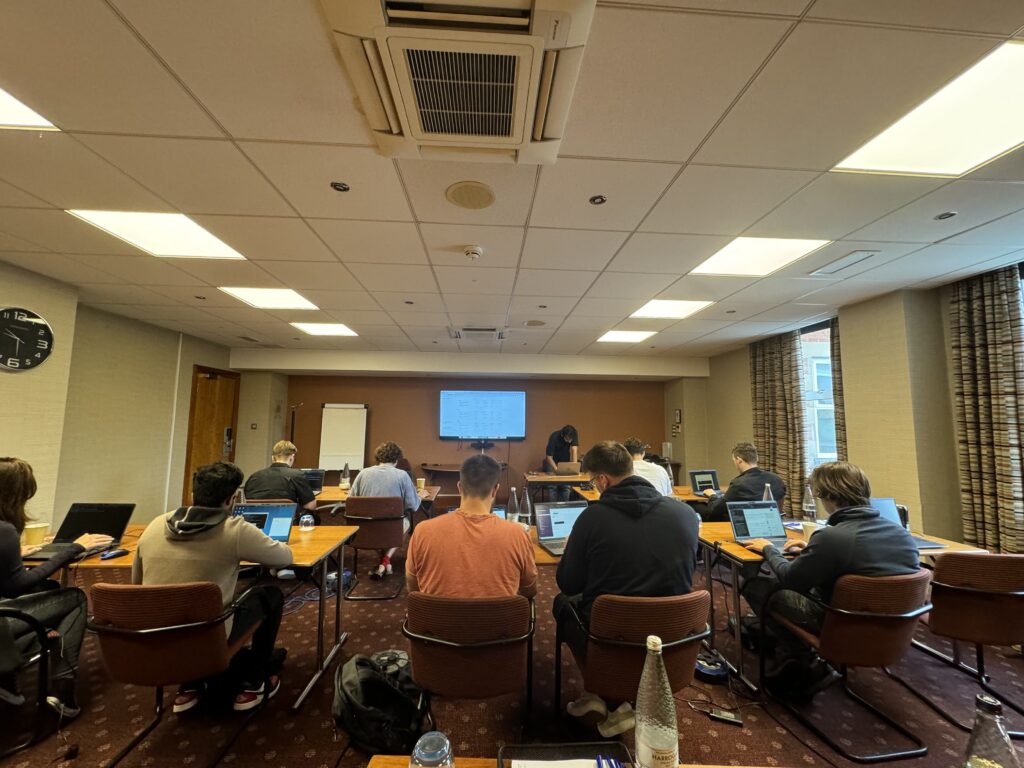
- Live On-Site
Who Should Attend?
Security researchers, penetration testers, iOS developers, and anyone looking to deeply understand iOS security internals.
Laptop Requirements
- • Laptop with 8+ GB RAM and 40 GB hard disk space
- • Students will be provided with access to cloud lab instances
- • Administrative access on the system
- • Detailed setup instructions sent before the course
We Train Anywhere in the World
Can't make it to a public event? We deliver on-site training directly at your location. Our instructors travel worldwide — tell us where you are.
Your country not listed? We still travel there.
Get in TouchTrusted Training Providers
Our trainers boast more than ten years of experience delivering diverse training sessions at conferences such as Blackhat, HITB, Power of Community, Zer0con, OWASP Appsec, and more.






Take Your Skills To The Next Level
Our Modes Of Training
On Demand
Learn at your own pace
Perfect for Self-Paced Learners
- Immediate access to materials
- Lecture recordings and self-assessments
- 365 days of access
- Certificate of completion
- Dedicated email support
- Certification exam
Live Virtual
Get in touch for pricing
Perfect for Teams in Multiple Locations
- Real-time interaction with expert trainers via Zoom
- Customizable content for your team
- Continued support after training
- Certification exam
Live On-Site
Get in touch for pricing
Perfect for Teams in One Location
- Real-time interaction at your onsite location
- Customizable content for your team
- Continued support after training
- Certification exam
FAQ
The information on this page is subject to change without notice.
Contact Us
Have a question or want to learn more about this training? Get in touch with us.
Our Location
51 Pleasant St # 843, Malden, MA, US, 02148
General Inquiries
contact@8ksec.io
Trainings
trainings@8ksec.io
