
Offensive ARM64 Reversing and Exploitation
Live On-Site / Live Virtual
Master Offensive ARM Exploitation
Get mastery in dissecting and manipulating ARM architecture-based systems for mobile security assessment. Learn the art of identifying vulnerabilities within ARM-based environments and crafting and executing sophisticated exploits, and unveiling security gaps within ARM64 based systems.

What You Will Learn
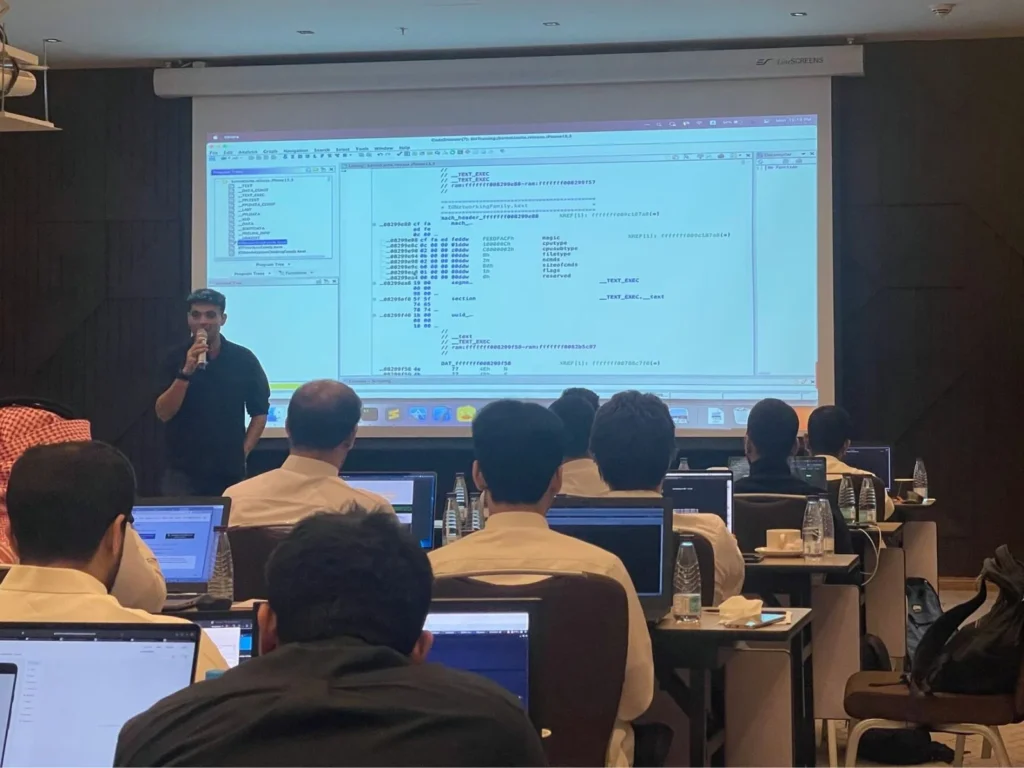
This course is designed for cybersecurity professionals and enthusiasts looking to master advanced techniques in ARM64 architecture. Starting with an in-depth exploration of ARM architecture, focusing on ARMv8 (64-bit) architecture and their historical evolution, participants will gain a solid understanding of the ARM64 instruction set, calling conventions, and architectural features. The course covers introduction to reverse engineering, providing essential concepts and methodologies for dissecting ARM binaries effectively. Participants will also receive hands-on training with Ghidra, a powerful reverse engineering tool, and learn how to leverage scripting to automate tasks and streamline analysis workflows.
Moving forward, the course covers various binary exploitation categories, such as Use-after-Free (UaF), Heap Overflow, and more. Participants will learn about exploit mitigations, including Address Space Layout Randomization (ASLR), Pointer Authentication Codes (PAC), Memory Tagging (MTE), Stack Canaries, and other defenses commonly encountered in modern systems. Students will also learn the art of writing JOP and ROP chains tailored for ARM architecture.
This course will be a mix of lectures, practical labs, and projects designed to give students hands-on experience with ARM64 architecture. Students will gain the skills needed to reverse engineer, identify vulnerabilities and create exploits for ARM64 binaries.
Key Objectives
- ✓ARM64 architecture fundamentals, including instruction set and conventions
- ✓Introduction to Ghidra and scripting for reverse engineering
- ✓Exploitation categories: UaF, Heap Overflow, and more
- ✓Mitigations like ASLR, PAC, Stack Canaries, etc., explained
- ✓Exploiting Info leaks to bypass ASLR
- ✓Exploiting Uninitialized Stack Variables for privilege escalation
- ✓Off-by-one byte overflow vulnerabilities and exploitation techniques
- ✓Advanced exploitation tactics: ROP, JOP, and chaining strategies
- ✓Constructing Jump-Oriented Programming (JOP) chains for ARM64
- ✓Advanced Dynamic Instrumentation using Frida
- ✓Firmware reversing for ARM64-based systems
- ✓Exploiting IoT devices: firmware, protocol analysis, and exploitation
All our live trainings are highly customizable. We can tailor the content to cover topics specific to your team's needs. Contact us for more details.
Syllabus
Module 1: Fundamentals of ARM64 Exploitation +
- •Overview of ARM64 architecture and instruction set
- •Introduction to ARM64 security mitigations
- •Understanding ARM64 calling convention
- •System specific Proprietary registers
- •Setting up a testing environment for ARM64 research
- •Overview of the different Binary Formats (Mach-O, ELF)
- •Segments and Sections in different Binary formats
- •ARM64 virtual memory management in mobile devices
Module 2: Reverse Engineering Essentials for ARM64 +
- •Key concepts and terminologies in reverse engineering
- •Introduction to reverse engineering tools like Hopper and Ghidra for ARM64
- •Exploring the ARM64 instruction set in depth
- •Analyzing and bypassing ARM64 security mitigations
- •Deep dive into ARM64 calling convention
- •Reversing sample binaries on ARM64 architecture
- •Disassembling methods and analyzing assembly instructions
- •Modifying assembly instructions for ARM64 exploitation
- •Deciphering Mangled Symbols in ARM64 binaries
Module 3: Advanced Exploitation Techniques for ARM64 +
- •Exploiting Heap Overflow in ARM64 binaries
- •Exploiting uninitialized stack variables in ARM64 binaries
- •Leveraging off-by-one byte overflow vulnerabilities for ARM64 exploitation
- •Constructing Jump-Oriented Programming (JOP) chains for ARM64
- •Crafting Return-Oriented Programming (ROP) chains for ARM64 binaries
- •Understanding and exploiting Uninitialized Memory vulnerabilities in ARM64 code
- •Analyzing and exploiting JOP (Jump-Oriented Programming) chains in ARM64 binaries
- •Exploiting ARM64-specific vulnerabilities and attack vectors
Module 4: Real-World Application and IoT Device Exploitation +
- •Applying ARM64 exploitation techniques to real-world applications and systems
- •Exploiting IoT devices powered by ARM64 architecture
- •Firmware reversing and exploitation on ARM64-based devices
- •Analyzing protocols and performing exploitation on ARM64 IoT devices
- •Hands-on labs and practical exercises simulating real-world ARM64 exploitation scenarios
- •Capture the Flag
Prerequisites
To successfully participate in this course, attendees should possess the following:
- • Working knowledge of cybersecurity and pentesting fundamentals
- • Basic Linux skills and command-line proficiency
- • Understanding of fundamental programming concepts and looping structures in at least one higher-level language (Java, Kotlin, Objective-C, Swift, C, C++, or similar)
- • Basic ARM/AARCH64 binary assembly and exploitation knowledge is recommended, but not required
- • Basic working knowledge of iOS and Android platforms is recommended, but not required
Offensive ARM Exploitation Expert (OAAE)
This course prepares you for the OAAE certification exam, a hands-on assessment specifically designed to test your grasp of advanced ARM64 reversing and exploitation knowledge.
EXAM DURATION: 48 Hours
Learn More
Duration
2 Days
Ways To Learn
- Live Virtual
- Live On-Site
Who Should Attend?
This course is specifically designed with the needs of modern exploit development and reverse engineering. This course will also be applicable for vulnerability researchers, penetration testers, mobile developers, or anyone keen to learn more about the ARM64 ecosystem.
Laptop Requirements
- • Laptop with: 8+ GB RAM and 40 GB hard disk space
- • Students will be provided with access to Linux cloud instances
- • Students will be provided with access to virtual ARM64 devices for hands-on and as such do not need to carry any physical devices
- • Administrative access on the system
- • Detailed Course Setup instructions and Slack access will be sent a few weeks prior to the class
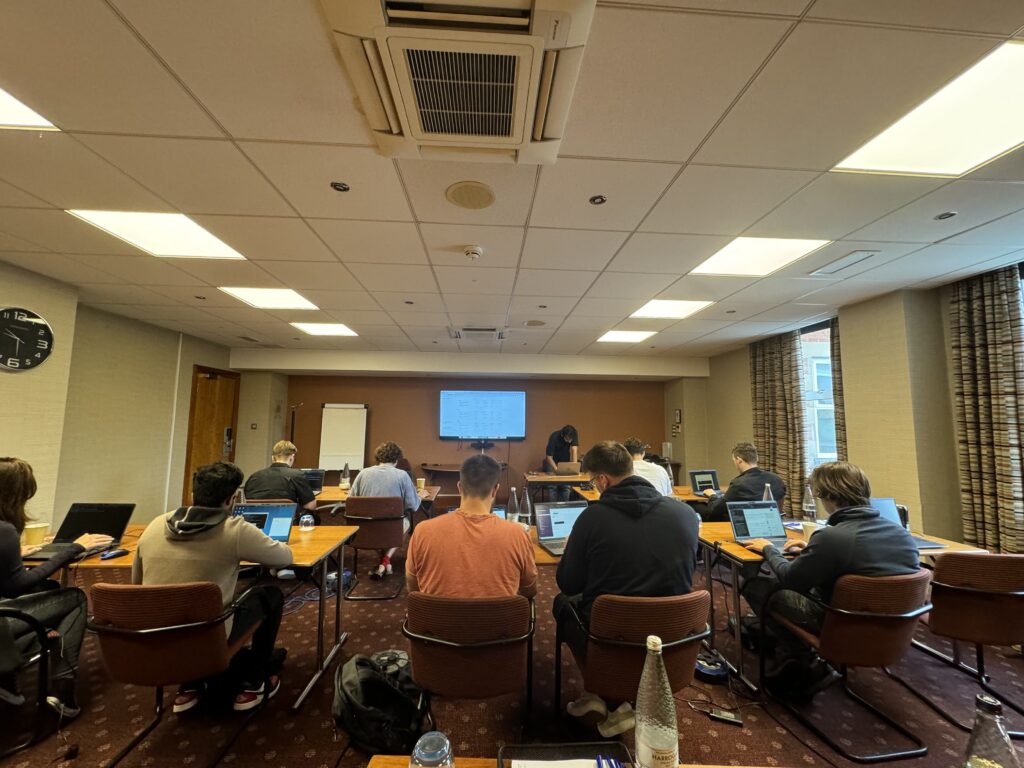
We Train Anywhere in the World
Can't make it to a public event? We deliver on-site training directly at your location. Our instructors travel worldwide — tell us where you are.
Your country not listed? We still travel there.
Get in TouchTrusted Training Providers
Our trainers boast more than ten years of experience delivering diverse training sessions at conferences such as Blackhat, HITB, Power of Community, Zer0con, OWASP Appsec, and more.






Take Your Skills To The Next Level
Our Modes Of Training
Live Virtual
Get in touch for pricing
Perfect for Teams in Multiple Locations
- Real-time interaction with expert trainers via Zoom
- Customizable content for your team
- Continued support after training
- Certification exam
Live On-Site
Get in touch for pricing
Perfect for Teams in One Location
- Real-time interaction at your onsite location
- Customizable content for your team
- Continued support after training
- Certification exam
FAQ
The information on this page is subject to change without notice.
Contact Us
Have a question or want to learn more about this training? Get in touch with us.
Our Location
51 Pleasant St # 843, Malden, MA, US, 02148
General Inquiries
contact@8ksec.io
Trainings
trainings@8ksec.io
