
Windows Malware Analysis and Memory Forensics
Live On-Site / Live Virtual
Master Windows Malware Analysis
Learn static, dynamic, code and memory analysis with practical labs on real-world malware samples. Uncover adversaries' tactics and integrate analysis into automated systems.
What You Will Learn
This course takes you through the complete Windows malware analysis lifecycle, from initial static triage to advanced memory forensics. You will learn to examine PE file structures, analyze imports and exports, detect packing and obfuscation, and write YARA rules for malware classification. Each technique is reinforced with hands-on labs using real-world malware samples.
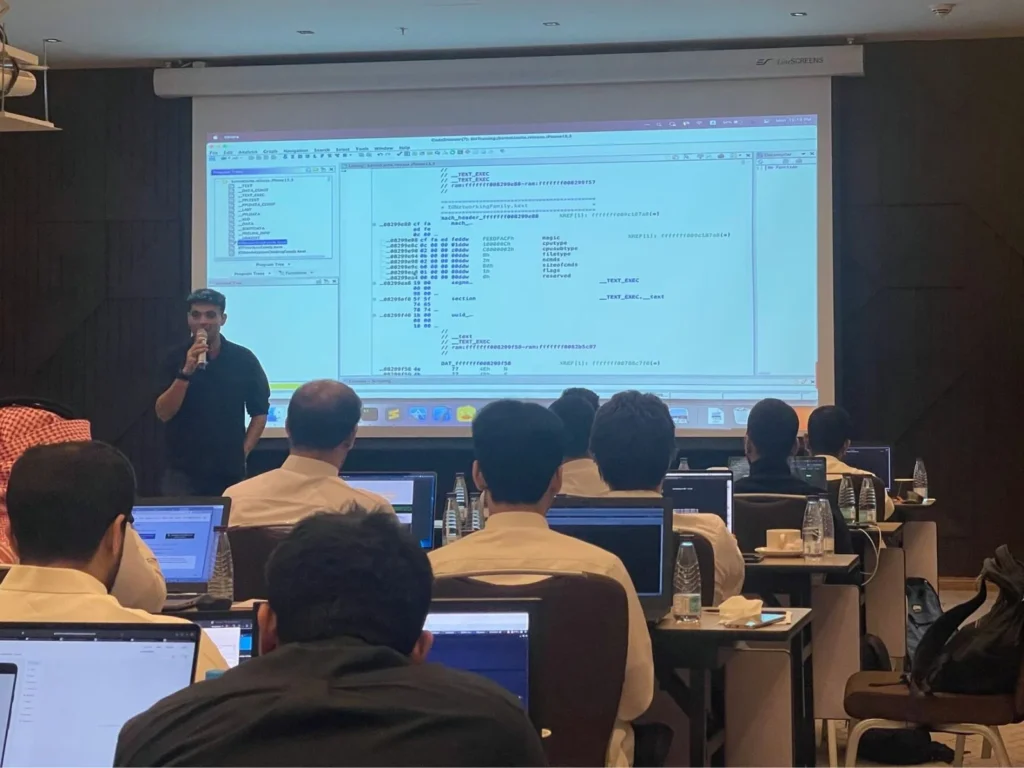
The dynamic analysis portion covers sandbox setup, behavioral monitoring, API hooking, process monitoring, and network activity capture. You will learn to use IDA Pro and Ghidra for code analysis, understand x86/x64 assembly, navigate control flow graphs, defeat anti-debugging techniques, and unpack protected malware. Real-world case studies include ransomware, APT malware, and fileless threats.
The memory forensics section introduces the Volatility framework for process analysis, DLL injection detection, rootkit discovery, and memory artifact extraction. You will also learn network-level analysis of C2 communications, protocol dissection, traffic decryption, and DNS analysis. The course concludes with automated analysis pipelines and threat intelligence integration to bring your skills into production workflows.
Key Objectives
- ✓Analyze PE file format including headers, imports, exports, and resources
- ✓Detect packing, obfuscation, and write YARA rules for classification
- ✓Set up safe sandbox environments for dynamic analysis
- ✓Monitor behavior including API calls, registry changes, and network activity
- ✓Use IDA Pro and Ghidra for code analysis and reverse engineering
- ✓Understand x86/x64 assembly and navigate control flow
- ✓Defeat anti-debugging techniques and unpack protected malware
- ✓Perform memory forensics with Volatility framework
- ✓Detect DLL injection, rootkits, and memory-resident threats
- ✓Analyze C2 communications, DNS activity, and encrypted traffic
- ✓Analyze ransomware, APT malware, and fileless threats
- ✓Build automated analysis pipelines with threat intelligence integration
All our live trainings are highly customizable. We can tailor the content to cover topics specific to your team's needs. Contact us for more details.
Syllabus
Module 1: Static Analysis Fundamentals +
- •PE file format: headers, sections, and overlays
- •Import and export table analysis
- •String analysis and embedded resource extraction
- •Packing detection and identification
- •YARA rule creation and malware classification
- •Hash-based identification and threat intelligence lookups
Module 2: Dynamic Analysis +
- •Sandbox setup and safe execution environment
- •Behavioral monitoring with Process Monitor and API Monitor
- •API hooking and function interception
- •Process creation and injection monitoring
- •Registry modification tracking
- •Network activity capture and analysis
Module 3: Code Analysis & Debugging +
- •IDA Pro and Ghidra fundamentals
- •x86/x64 assembly language essentials
- •Control flow analysis and graph navigation
- •Anti-debugging techniques and countermeasures
- •Unpacking protected and obfuscated malware
- •Debugging with x64dbg and WinDbg
Module 4: Memory Forensics +
- •Volatility framework setup and usage
- •Process analysis and hidden process detection
- •DLL injection detection and analysis
- •Rootkit detection in memory
- •Memory artifact extraction and analysis
- •Reconstructing malware behavior from memory dumps
Module 5: Network Analysis +
- •C2 communication identification and analysis
- •Protocol analysis and dissection
- •Traffic decryption techniques
- •DNS analysis and domain generation algorithms
- •Malware communication patterns and beaconing
- •Network IOC extraction
Module 6: Advanced Topics +
- •Ransomware analysis and decryption techniques
- •APT malware analysis and attribution
- •Fileless malware detection and analysis
- •Automated analysis pipelines and tooling
- •Threat intelligence integration and sharing
- •Building detection signatures from analysis findings
Prerequisites
To successfully participate in this course, attendees should possess the following:
- • Working knowledge of cybersecurity fundamentals
- • Basic Windows administration familiarity
- • Basic command-line and PowerShell proficiency
- • Understanding of x86/x64 assembly helpful but not required
Duration
3 Days
Ways To Learn
- Live Virtual
- Live On-Site
Who Should Attend?
Malware analysts, incident responders, SOC analysts, threat hunters, and security researchers.
Laptop Requirements
- • Laptop with 8+ GB RAM and 40 GB hard disk space
- • Students will be provided with access to cloud lab instances
- • Administrative access on the system
- • Detailed setup instructions sent before the course
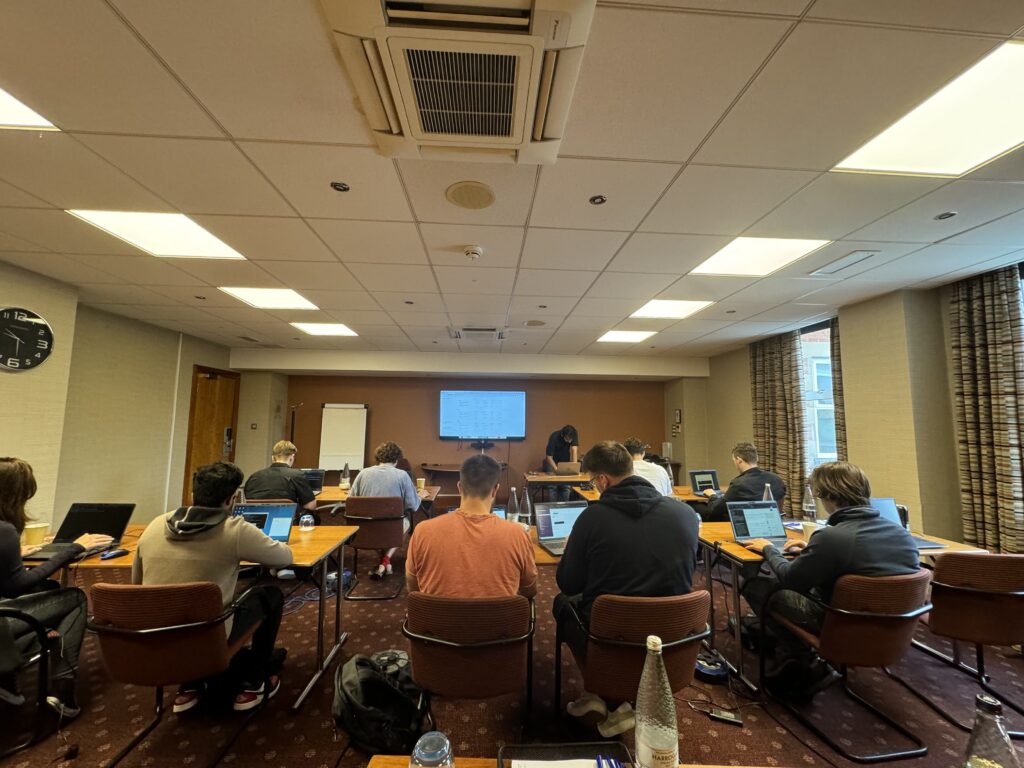
We Train Anywhere in the World
Can't make it to a public event? We deliver on-site training directly at your location. Our instructors travel worldwide — tell us where you are.
Your country not listed? We still travel there.
Get in TouchTrusted Training Providers
Our trainers boast more than ten years of experience delivering diverse training sessions at conferences such as Blackhat, HITB, Power of Community, Zer0con, OWASP Appsec, and more.






Take Your Skills To The Next Level
Our Modes Of Training
Live Virtual
Get in touch for pricing
Perfect for Teams in Multiple Locations
- Real-time interaction with expert trainers via Zoom
- Customizable content for your team
- Continued support after training
- Certificate of completion
Live On-Site
Get in touch for pricing
Perfect for Teams in One Location
- Real-time interaction at your onsite location
- Customizable content for your team
- Continued support after training
- Certificate of completion
FAQ
The information on this page is subject to change without notice.
Contact Us
Have a question or want to learn more about this training? Get in touch with us.
Our Location
51 Pleasant St # 843, Malden, MA, US, 02148
General Inquiries
contact@8ksec.io
Trainings
trainings@8ksec.io
