
Offensive IoT Firmware Reversing and Analysis
Live On-Site / Live Virtual
Master Firmware Reverse Engineering for IoT Devices
Learn to extract, analyze, and exploit IoT firmware using industry-standard reverse engineering tools. This hands-on course covers hardware-level firmware acquisition, static and dynamic analysis with IDA Pro / Ghidra / Binary Ninja, and practical vulnerability discovery across ARM64 and MIPS targets.
What You Will Learn
IoT devices are everywhere — from smart home appliances and IP cameras to industrial controllers and automotive systems. The firmware running on these devices is often the weakest link in the security chain, yet analyzing it requires a unique blend of hardware knowledge, reverse engineering skills, and embedded systems expertise. This course bridges that gap.
You will learn the complete firmware analysis lifecycle: acquiring firmware through hardware interfaces (UART, JTAG, SPI flash) and software channels (OTA interception, vendor downloads), unpacking and extracting filesystems, reverse engineering binaries compiled for ARM64 and MIPS architectures using IDA Pro / Ghidra / Binary Ninja, and discovering real vulnerabilities in production IoT firmware.
The course emphasizes practical, hands-on methodology. You will analyze firmware from real-world devices, write custom analysis scripts, emulate firmware for dynamic testing using QEMU and Firmadyne, and practice exploitation techniques specific to embedded environments. By the end of the course, you will have a repeatable methodology for assessing any IoT device's firmware security posture.
Key Objectives
- ✓Extract firmware from IoT devices using UART, JTAG, SWD, and SPI flash interfaces
- ✓Unpack and analyze firmware filesystems using Binwalk, Unblob, and EMBA
- ✓Reverse engineer ARM64 and MIPS binaries using IDA Pro / Ghidra / Binary Ninja
- ✓Write custom analysis scripts in IDAPython, Ghidra Python, and Binary Ninja API
- ✓Emulate firmware for dynamic analysis using QEMU and Firmadyne
- ✓Identify and exploit common IoT vulnerabilities: command injection, buffer overflows, hardcoded credentials, and insecure update mechanisms
- ✓Analyze bootloader security, secure boot chains, and firmware encryption schemes
- ✓Assess IoT protocol security (MQTT, CoAP, BLE, Zigbee) and cloud backend interfaces
- ✓Perform hardware-assisted debugging with JTAG and SWD
- ✓Build a repeatable IoT firmware security assessment methodology
All our live trainings are highly customizable. We can tailor the content to cover topics specific to your team's needs. Contact us for more details.
Syllabus
Module 1: IoT Security Landscape and Firmware Fundamentals +
- •IoT attack surface overview — device, network, cloud, and mobile companion apps
- •Firmware types: monolithic, RTOS-based, embedded Linux, bare-metal
- •Common IoT SoC platforms and their security features
- •ARM64 (AArch64) architecture primer — registers, calling conventions, instruction set
- •MIPS architecture primer — GP-relative addressing, delay slots, PIC code
- •Embedded Linux boot flow — U-Boot, kernel, rootfs, init systems
- •Introduction to the lab environment and toolchain setup
Module 2: Hardware-Level Firmware Extraction +
- •Identifying debug interfaces on PCBs — UART, JTAG, SWD, SPI, I2C headers
- •UART serial console access — baud rate detection, shell acquisition
- •JTAG and SWD debugging — OpenOCD, J-Link, boundary scan
- •SPI flash dumping — using Flashrom, Bus Pirate, and dedicated readers
- •eMMC and NAND flash extraction techniques (ISP method)
- •Software-based acquisition — OTA update interception, vendor portal downloads, update protocol analysis
- •Dealing with encrypted firmware — identifying encryption, key extraction strategies
- •Lab: Extract firmware from a real device image via UART and SPI flash dump
Module 3: Firmware Unpacking and Filesystem Analysis +
- •Firmware image structure — headers, partitions, filesystem offsets
- •Unpacking with Binwalk — entropy analysis, signature scanning, recursive extraction
- •Unblob for modern firmware containers — advantages over Binwalk for nested formats
- •Filesystem types — SquashFS, JFFS2, UBIFS, CramFS, ext4, YAFFS2
- •Automated firmware scanning with EMBA — SBOM generation, credential detection, configuration analysis
- •Manual filesystem triage — passwd/shadow files, SSH keys, API tokens, certificates
- •Identifying third-party libraries and SDK components in stripped binaries
- •Buildroot and Yocto-based firmware identification and analysis
- •Lab: Unpack router firmware, extract filesystem, and perform automated triage with EMBA
Module 4: Reverse Engineering IoT Firmware with IDA Pro / Ghidra / Binary Ninja +
- •Loading ARM64 and MIPS firmware binaries — processor options, memory layout, and base address configuration in IDA Pro / Ghidra / Binary Ninja
- •Navigating stripped binaries — function identification, cross-references, and string analysis
- •Decompiler workflows — reading and annotating pseudocode with Hex-Rays (IDA Pro), Ghidra Decompiler, and Binary Ninja HLIL
- •Library identification in stripped firmware — FLIRT signatures (IDA Pro), Function ID (Ghidra), and signature libraries (Binary Ninja)
- •MIPS-specific analysis — handling GP-relative addressing and PIC relocations
- •SVD Loader and peripheral register annotation — mapping MMIO addresses to named registers
- •Loading bare-metal firmware — raw binary blobs, defining memory regions, architecture-specific settings
- •Comparing IDA Pro, Ghidra, and Binary Ninja — strengths, weaknesses, and when to use each
- •Lab: Reverse engineer an ARM64 IoT service binary using IDA Pro / Ghidra / Binary Ninja to identify an authentication bypass
Module 5: Scripting and Automated Analysis with IDA Pro / Ghidra / Binary Ninja +
- •IDAPython scripting — automating analysis, finding dangerous function calls (system, popen, strcpy), annotating MMIO regions
- •Ghidra scripting with Python (Ghidrathon) and Java — batch analysis, vulnerability pattern detection
- •Binary Ninja Python API — using BNIL intermediate language and SSA form for data flow analysis
- •Writing custom plugins for IoT-specific analysis tasks in IDA Pro / Ghidra / Binary Ninja
- •Taint tracking from user input to dangerous sinks across all three tools
- •Cross-tool workflows — exporting annotations and sharing analysis results between tools
- •AI-assisted binary analysis — using LLMs for function naming and decompilation comprehension
- •Lab: Write a script (IDAPython / Ghidra Python / Binary Ninja API) to identify unsafe function usage patterns across an entire firmware image
Module 6: Dynamic Analysis and Firmware Emulation +
- •Full-system firmware emulation with Firmadyne and FirmAE — automated network configuration
- •QEMU user-mode emulation for individual ARM64 and MIPS binaries
- •QEMU system-mode emulation — booting full firmware images
- •Remote debugging with IDA Pro / Ghidra / Binary Ninja — GDB server integration, breakpoints, memory inspection
- •Intercepting and analyzing network traffic from emulated firmware
- •Overcoming emulation challenges — NVRAM simulation, peripheral stubs, kernel module dependencies
- •OFRAK for programmatic firmware modification and repacking
- •Lab: Emulate an IoT device firmware with Firmadyne, attach IDA Pro / Ghidra / Binary Ninja debugger, and trace a web request through the CGI handler
Module 7: IoT Firmware Vulnerability Discovery +
- •Command injection in web interfaces and CGI handlers — identifying sinks (system, popen, exec) and tracing user input with IDA Pro / Ghidra / Binary Ninja
- •Buffer overflows in embedded C services — stack overflows, heap corruption, format string vulnerabilities
- •Hardcoded credentials and backdoor accounts — systematic discovery techniques
- •Insecure firmware update mechanisms — missing signature verification, downgrade attacks, TOCTOU races
- •Cryptographic weaknesses — weak keys, known default keys, plaintext secret storage, custom crypto
- •Authentication and authorization flaws in management interfaces
- •Information leakage — debug endpoints, verbose error messages, exposed internal APIs
- •Lab: Discover and chain multiple vulnerabilities in an IoT device firmware to achieve remote code execution
Module 8: Exploitation Techniques for Embedded Targets +
- •Stack-based exploitation on ARM64 — ROP chain construction, gadget finding, return-to-libc
- •MIPS-specific exploitation — cache incoherency challenges, branch delay slot abuse, shellcode considerations
- •Bypassing exploit mitigations in embedded firmware — understanding what protections are (and aren't) present
- •ARM64 pointer authentication (PAC) and branch target identification (BTI) — when present and how they affect exploitation
- •Writing cross-architecture shellcode for ARM64 and MIPS
- •Post-exploitation on embedded Linux — persistence, lateral movement to other devices, credential harvesting
- •Lab: Exploit a buffer overflow in an emulated MIPS router service to gain a reverse shell
Module 9: Bootloader and Secure Boot Analysis +
- •U-Boot internals — environment variables, boot commands, shell access
- •U-Boot exploitation — environment variable manipulation, memory read/write primitives
- •Secure boot chain analysis — hardware root of trust, chain of trust verification
- •TF-A (Trusted Firmware-A) and OP-TEE analysis for ARM64 platforms
- •Reversing bootloader code with IDA Pro / Ghidra / Binary Ninja
- •Bypassing secure boot — fault injection concepts, signed image manipulation, key extraction
- •Firmware encryption and decryption — AES-CBC, XOR-based schemes, key recovery from bootloader
- •Lab: Analyze a U-Boot bootloader using IDA Pro / Ghidra / Binary Ninja to extract encryption keys and decrypt a firmware image
Module 10: IoT Protocol and Network Security Analysis +
- •MQTT broker security — authentication bypass, topic enumeration, message interception
- •CoAP protocol analysis — request forgery, resource discovery, DTLS weaknesses
- •BLE (Bluetooth Low Energy) security — GATT characteristic abuse, sniffing, replay attacks
- •Zigbee and Matter/Thread protocol security overview
- •Cloud API backend analysis — identifying device-to-cloud communication endpoints and authentication flaws
- •Firmware supply chain risks — third-party SDK audit, ODM firmware analysis, SBOM generation
- •Lab: Intercept and analyze MQTT traffic from emulated firmware to identify information disclosure
Module 11: Assessment Methodology and Reporting +
- •Building a repeatable IoT firmware assessment methodology — from device acquisition to final report
- •Threat modeling IoT devices — STRIDE applied to firmware, hardware interfaces, and communication channels
- •OWASP IoT Top 10 — mapping findings to industry-standard vulnerability categories
- •Writing effective firmware security assessment reports — technical detail, risk rating, remediation guidance
- •Responsible disclosure for IoT vulnerabilities — vendor coordination challenges, coordinated disclosure timelines
- •Regulatory landscape — security requirements for IoT devices (EU Cyber Resilience Act, NIST guidelines, ETSI EN 303 645)
- •Capstone Lab: End-to-end firmware security assessment — extract, analyze with IDA Pro / Ghidra / Binary Ninja, discover vulnerabilities, and produce a professional report
Prerequisites
To successfully participate in this course, attendees should possess the following:
- • Solid understanding of Linux command-line and system administration
- • Basic knowledge of C/C++ programming and reading source code
- • Familiarity with at least one disassembler or debugger (IDA Pro, Ghidra, Binary Ninja, GDB, or similar)
- • Understanding of computer architecture fundamentals (registers, memory, stack)
- • Basic networking knowledge (TCP/IP, HTTP, common protocols)
- • Prior experience with embedded systems or IoT devices is helpful but not required
Duration
3 Days
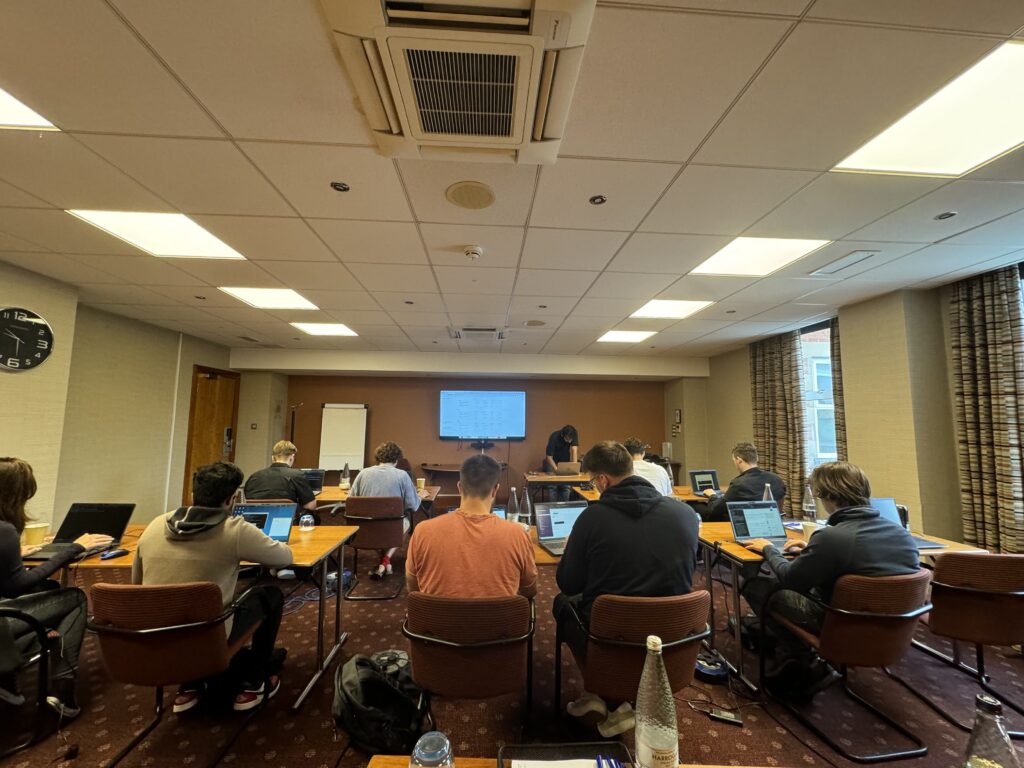
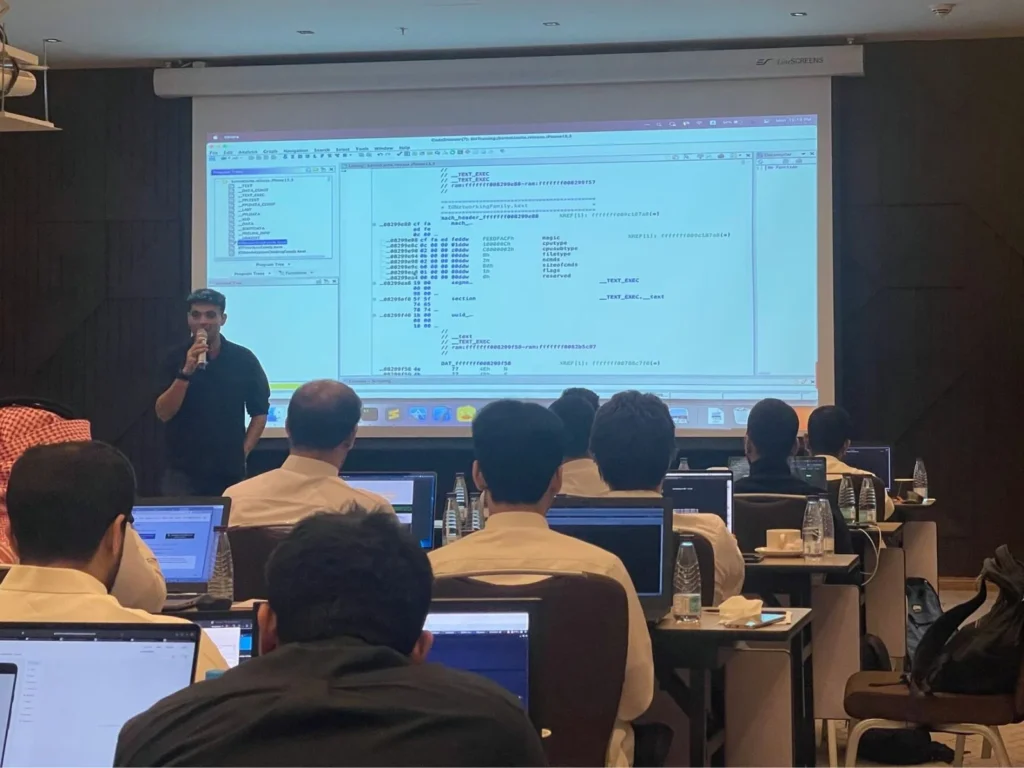
Ways To Learn
- Live Virtual
- Live On-Site
Who Should Attend?
Security researchers, penetration testers, embedded systems engineers, vulnerability analysts, and reverse engineers who want to build practical skills in IoT firmware security assessment.
Laptop Requirements
- • Laptop with 16+ GB RAM and 60 GB free disk space
- • Administrative/root access on the system
- • At least one of the following disassemblers installed: IDA Pro, Ghidra, or Binary Ninja (trial licenses acceptable — setup instructions sent before the course)
- • Cloud lab instances provided for hardware emulation exercises
- • Setup instructions and pre-course materials sent 2 weeks before the course
We Train Anywhere in the World
Can't make it to a public event? We deliver on-site training directly at your location. Our instructors travel worldwide — tell us where you are.
Your country not listed? We still travel there.
Get in TouchTrusted Training Providers
Our trainers boast more than ten years of experience delivering diverse training sessions at conferences such as Blackhat, HITB, Power of Community, Zer0con, OWASP Appsec, and more.






Take Your Skills To The Next Level
Our Modes Of Training
Live Virtual
Get in touch for pricing
Perfect for Teams in Multiple Locations
- Real-time interaction with expert trainers via Zoom
- Customizable content for your team
- Continued support after training
- Hands-on labs with cloud environments and real device firmware
Live On-Site
Get in touch for pricing
Perfect for Teams in One Location
- Real-time interaction at your onsite location
- Customizable content for your team
- Continued support after training
- Hands-on labs with physical hardware and cloud environments
FAQ
The information on this page is subject to change without notice.
Contact Us
Have a question or want to learn more about this training? Get in touch with us.
Our Location
51 Pleasant St # 843, Malden, MA, US, 02148
General Inquiries
contact@8ksec.io
Trainings
training@8ksec.io
